How to configure SSH Two Factor Authentication on Ubuntu 22.04
Introduce
SSH Two Factor Authentication, also known as 2-Step Authentication for SSH service, with this feature, users can increase the security of their server from the risk of attacks via SSH protocol. And in this article, we will show you how to install Google Authenticator and configure Two Factor Authentication when SSHing into a system using Ubuntu 22.04.
Installation Instructions
Step 1: Install and Configure Google Authenticator
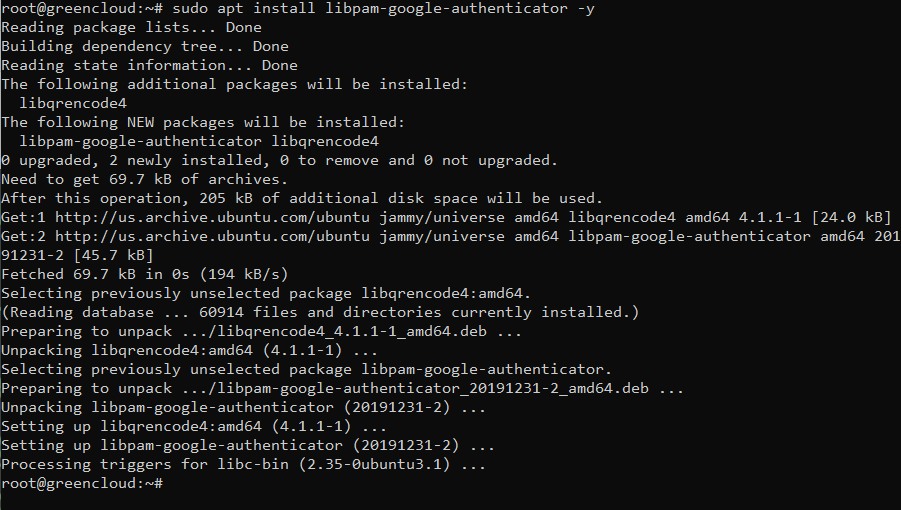
- To install Google Authenticator, go to your Ubuntu 22.04 server, and run the command:
sudo apt install libpam-google-authenticator -y
- Generate security code
To generate a security key, type the command
google-authenticator
After typing the above command, the result will appear a link and QR code as shown below.
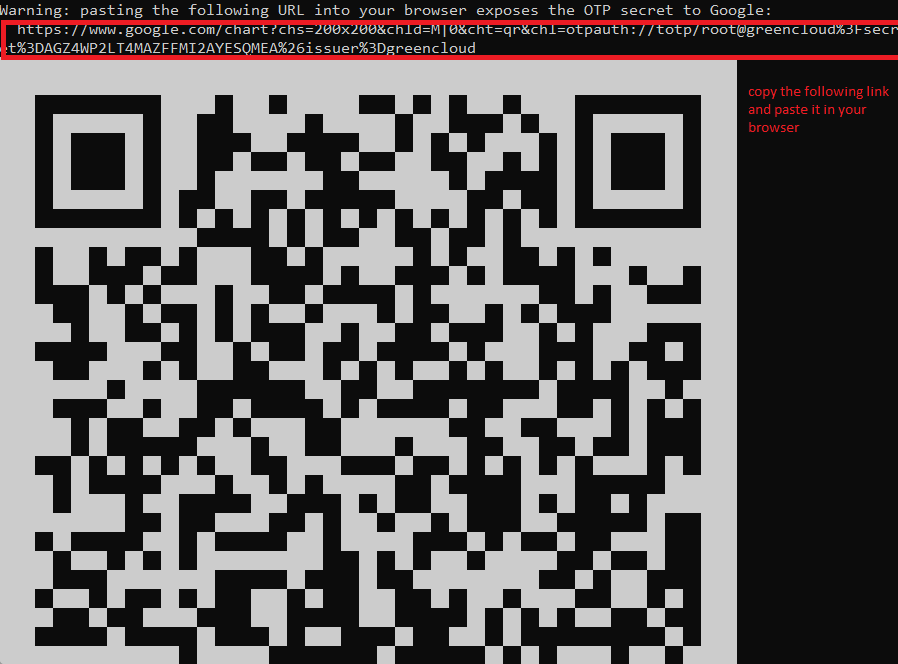
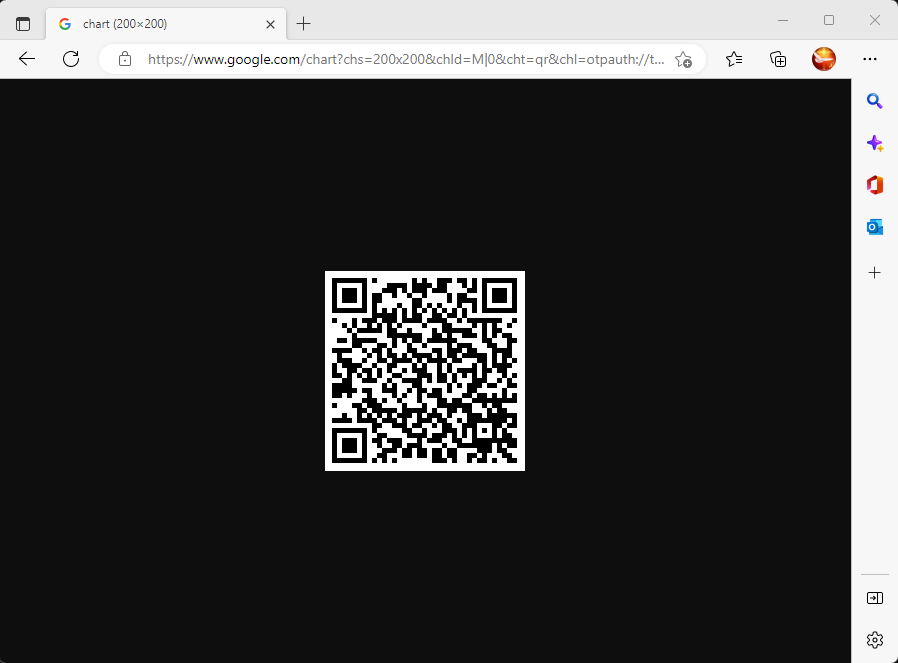
If the image is too big, then you can copy that link and paste it in the browser to display the QR code easier to see as below.
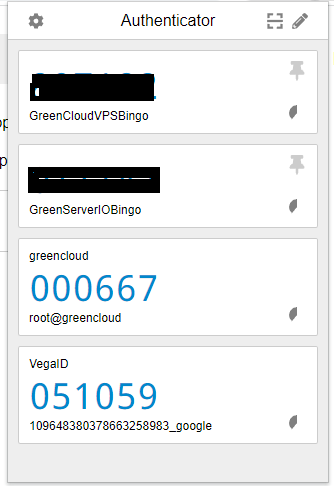
- You open App Authenticator and proceed to Scan the QR code displayed on your VPS.
When scanning the above QR code, we will receive a 6-digit code, these 6 digits will continuously change after 30 seconds.
After you have the above 6 numbers, you proceed with those 6 numbers to the server setup to complete the installation.

After successfully entering the code, you will receive an emergency code and need to verify some of the information below.
Code confirmed
Your emergency scratch codes are:
32788307
11480031
78992160
60171886
58985147
Do you want me to update your "/root/.google_authenticator" file? (y/n) y
Do you want to disallow multiple uses of the same authentication
token? This restricts you to one login about every 30s, but it increases
your chances to notice or even prevent man-in-the-middle attacks (y/n) y
By default, a new token is generated every 30 seconds by the mobile app.
In order to compensate for possible time-skew between the client and the server,
we allow an extra token before and after the current time. This allows for a
time skew of up to 30 seconds between authentication server and client. If you
experience problems with poor time synchronization, you can increase the window
from its default size of 3 permitted codes (one previous code, the current
code, the next code) to 17 permitted codes (the 8 previous codes, the current
code, and the 8 next codes). This will permit for a time skew of up to 4 minutes
between client and server.
Do you want to do so? (y/n) y
If the computer that you are logging into isn't hardened against brute-force
login attempts, you can enable rate-limiting for the authentication module.
By default, this limits attackers to no more than 3 login attempts every 30s.
Do you want to enable rate-limiting? (y/n) yStep 2: Configure OpenSSH to use 2FA
- Edit the configuration file at /etc/pam.d/sshd
First, backup the file with the command
sudo cp /etc/pam.d/sshd /etc/pam.d/sshd.bak
Then you edit the file with the command
sudo nano /etc/pam.d/sshd
Then just after the @include common-auth add the following line:
auth required pam_google_authenticator.so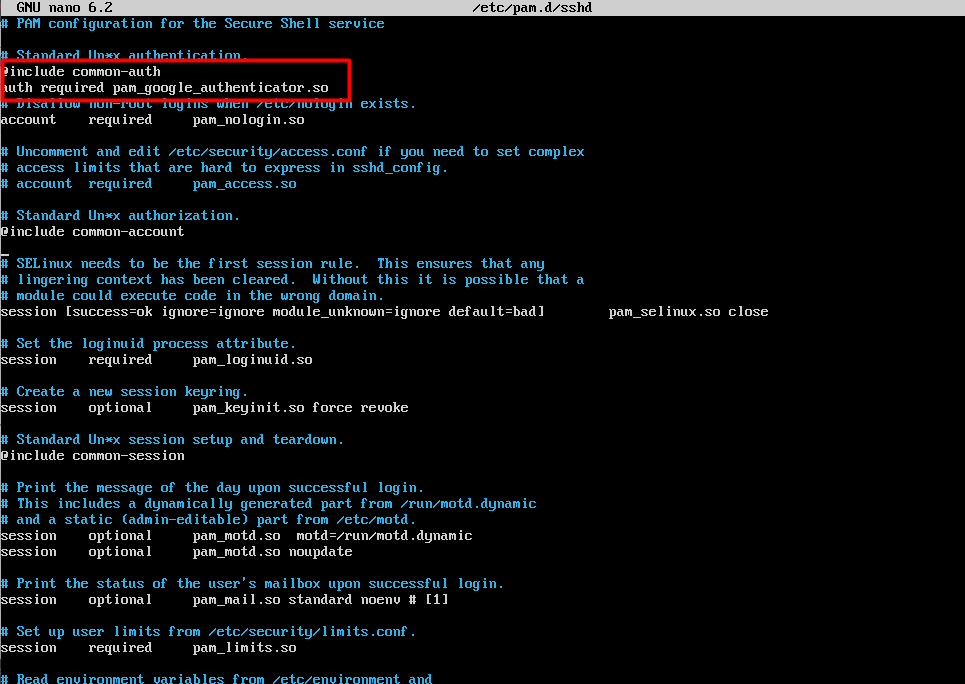
- Edit the configuration file at /etc/ssh/sshd_config
First, backup the file with the command
sudo cp /etc/ssh/sshd_config /etc/ssh/sshd_config.bak
Then you edit the file with the command
sudo nano /etc/ssh/sshd_config
Change the following two options to yes:
KbdInteractiveAuthentication yes
UsePAM yes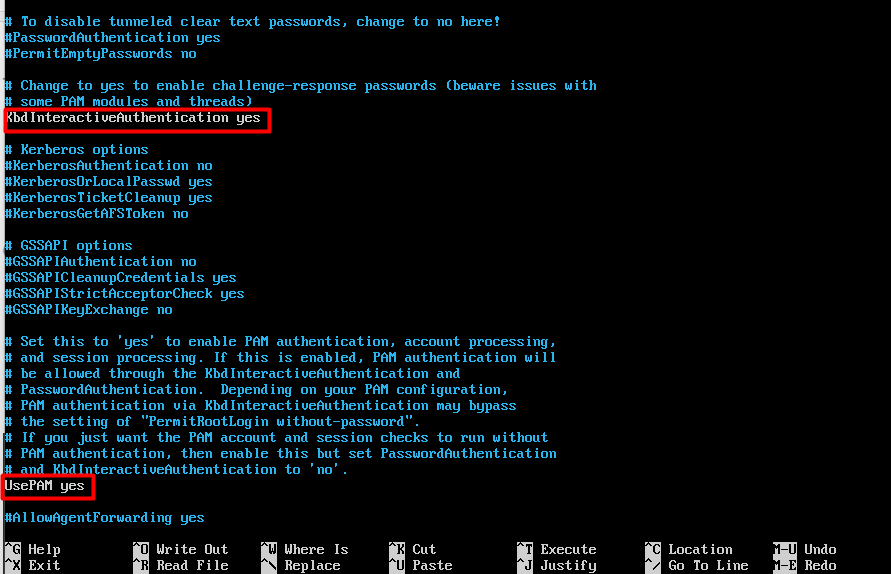
Restart the service
sudo systemctl restart sshd.service
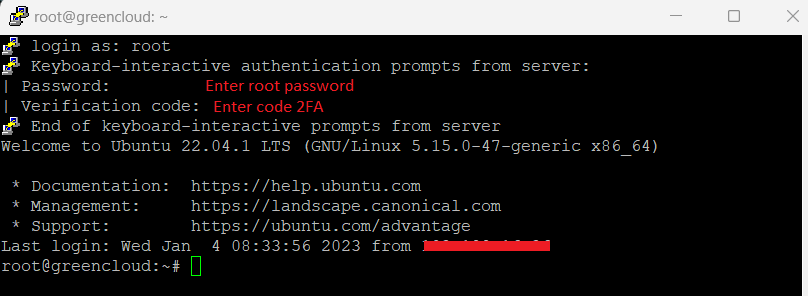
Step 3: SSH into the test server
After the configuration completes the steps, now you proceed to SSH into your Ubuntu 22.04 server to see the results. And as shown below, you can see that after I enter the Passwd root of the VPS, the system will ask to enter the 2-factor authentication code. Now you just need to check the Google Authenticator App to get the Code and enter it to be able to SSH successfully.
Summary
Through this article we have guided to configure SSH Two Factor Authentication on Ubuntu 22.04. Hope you do it successfully


