How to monitor Firewall activity with the Windows Firewall log
In the process of filtering Internet traffic, all firewalls have some type of logging feature that documents how the firewall handles various types of traffic. These logs can provide valuable information such as source and destination IP addresses, port numbers, and protocols. This article will help you monitor logs and Windows Firewall usage and control traffic easily.
How to Generate the Log File
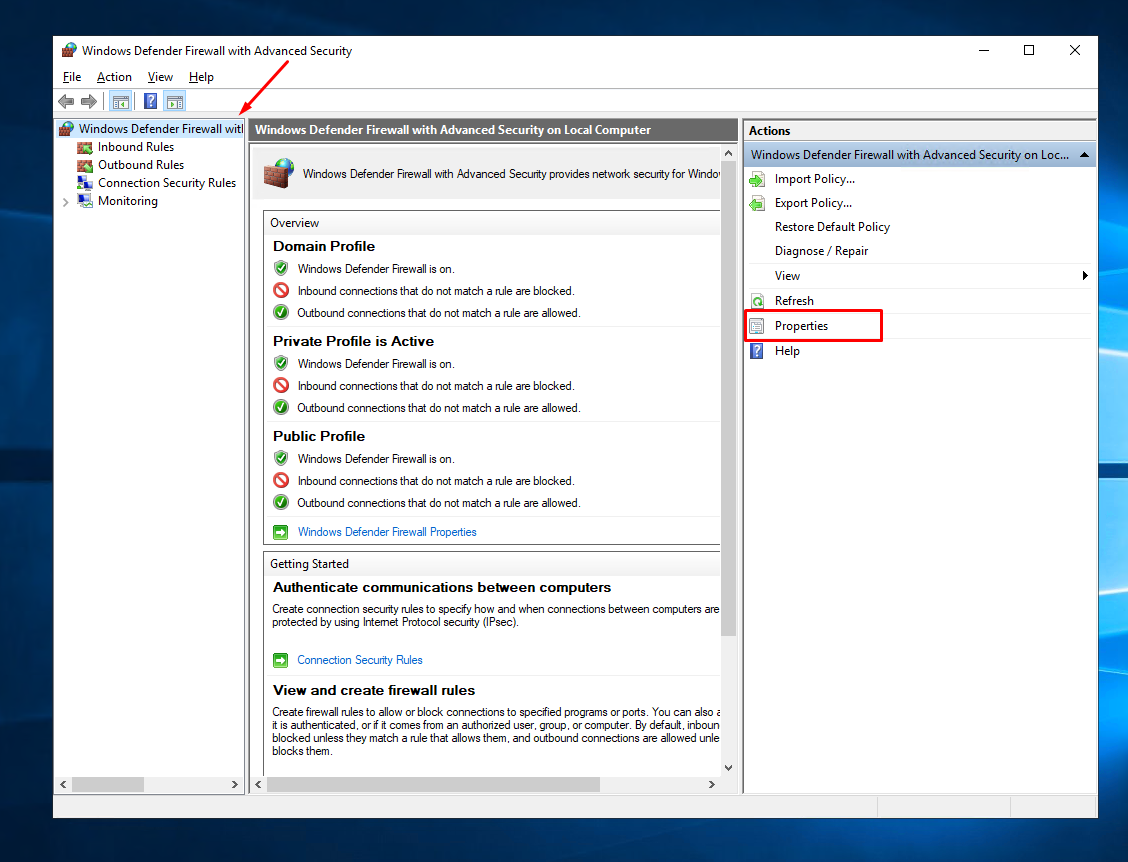
By default, the log file is disabled, which means that no information is written to the log file. To create a log file press “Win key + R” to open the Run box. Type “wf.msc” and press Enter. The “Windows Firewall with Advanced Security” screen appears. On the right side of the screen, click “Properties.”
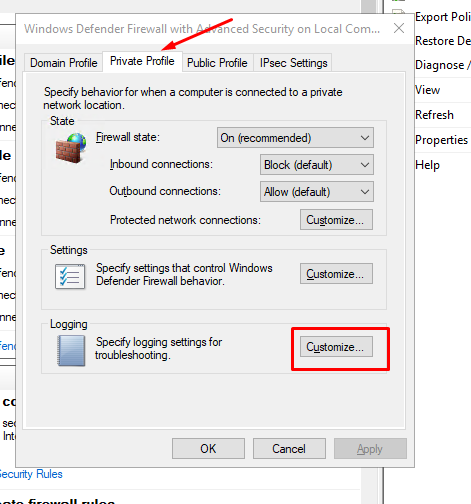
A new dialog box appears. Now click the “Private Profile” tab and select “Customize” in the “Logging Section”
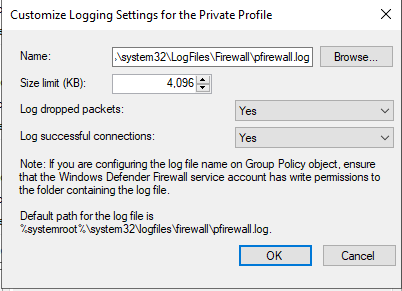
A new window opens and from that screen choose your maximum log size, location, and whether to log only dropped packets, successful connections or both. A dropped packet is a packet that Windows Firewall has blocked. Successful connections refer to both incoming connections as well as any connection you have made over the Internet, but it doesn’t always mean that an intruder has successfully connected to your computer.
Next, click the “Public Profile” tab and repeat the same steps you did for “Private Profile” tab.
You’ve now turned on the log for both private and public network connections.
Open Log File
On the main “Windows Firewall with Advanced Security” screen, scroll down until you see the “Monitoring” link. In the Details pane, under “Logging Settings”, click the file path next to “File Name.” The log opens in Notepad.
Interpreting the Windows Firewall log
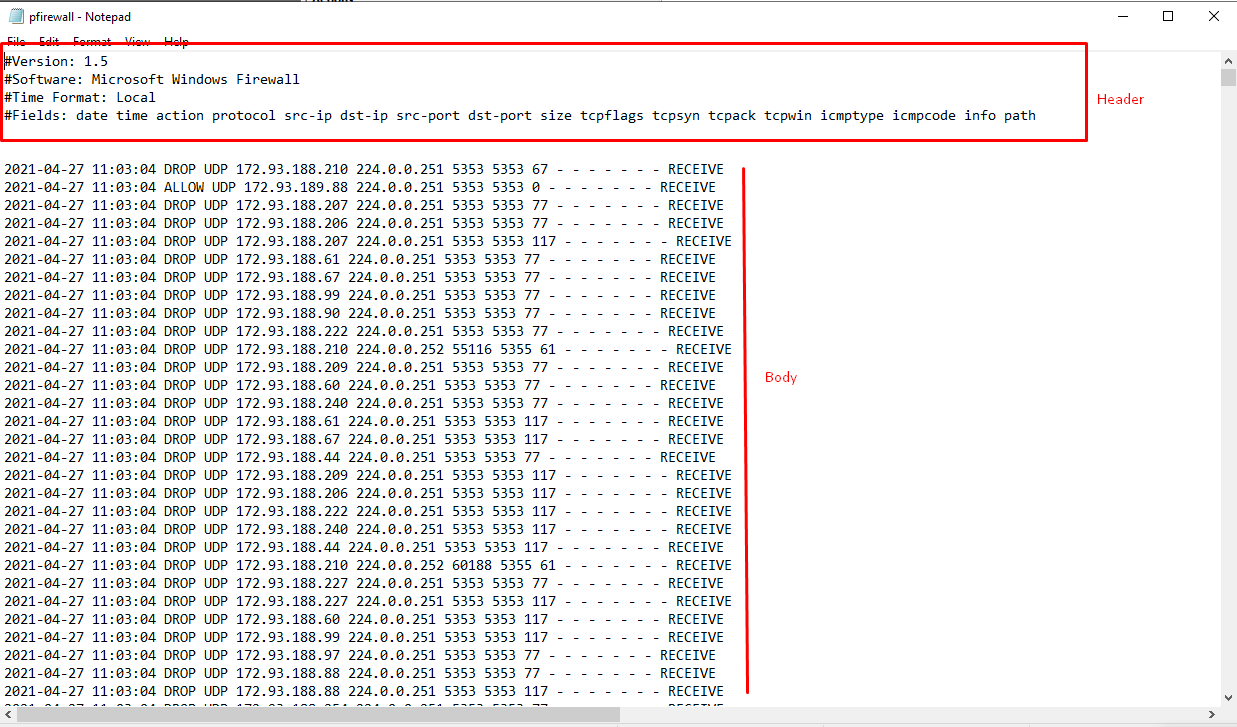
The Windows Firewall security log contains two sections. The header provides static, descriptive information about the version of the log, and the fields available. The body of the log is the compiled data that is entered as a result of traffic that tries to cross the firewall.
Here is the important information you need to pay attention to:
"2021-04-27 11:03:04" - Date and time of the connection. "ALLOW/DROP" - "Allow" which means that Firewall allows your connection through, "Drop" means Firewall do not allows your connection through "TCP/UDP" - Connection type (TCP or UDP) "RECEIVE/SEND" - Displays the direction of the communication