How to install FreeIPA Server on AlmaLinux 9
In this article, we discuss in detail the installation and configuration of the FreeIPA Server on the Rocky Linux 9 / AlmaLinux 9 system. FreeIPA is a popular and widely used identity management solution useful in managing user authentication, creation and enforcement of policies, identity stores, and authorization policies in a Linux domain. FreeIPA aims at eliminating the overhead for Linux Administrators working in medium to large-scale Linux-powered infrastructures.
Some of the advanced features of FreeIPA are:
- Support for large groups of Linux machines
- Has native integration with Windows Active Directory
- Advanced features of Linux operating system environments
- Full multi-master replication for higher redundancy and scalability
- Provision of extensible management interfaces (Web UI, CLI, XMLRPC, and JSON-RPC API) and Python SDK
Key Benefits of using FreeIPA:
- Central Authentication Management – Centralized management of users, machines, and services within large Linux/Unix enterprise environments.
- Fine-grained Access Control: Provides a clear method of defining access control policies to govern user identities and delegation of administrative tasks.
- One Time Password (OTP): Provides a popular method for achieving two-factor authentication (2FA).
- Direct Connect to Active Directory: You can retrieve information from Active Directory (AD) and join a domain or realm in a standard way.
- Active Directory Cross-Realm Trust: As a System Administrator, you can establish cross-forest Kerberos trusts with Microsoft Active Directory. This allows external Active Directory (AD) users convenient access to resources in the Identity Management domain.
- Integrated Public Key Infrastructure (PKI) Service: This provides PKI services that sign and publish certificates for hosts and services, Certificate Revocation List (CRL) and OCSP services for software validating the published certificate, and an API to request, show, and find certificates.
Install FreeIPA Server on Rocky Linux 9 / AlmaLinux 9
Ensure this installation is done on a freshly installed Rocky Linux 9 / AlmaLinux 9 system since IPA services ports could conflict with other Linux services.
1: Update system, set hostname
Update your Rocky Linux / AlmaLinux 9 server:
dnf -y update
rebootOnce rebooted, set the correct system hostname.
hostnamectl set-hostname greencloud.example.comThe host name must be a fully qualified domain name, such as ipa.example.com. Once set also configure the system timezone to match your region:
timedatectl set-timezone Africa/NairobiConfirm your timezone settings:
$ timedatectl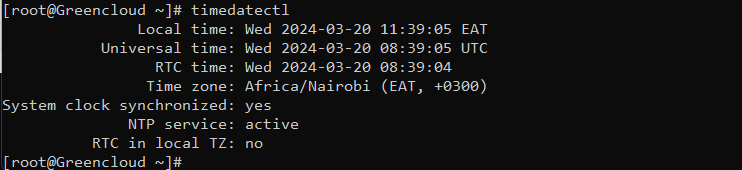
2: Check FreeIPA server installation pre-reqs
Key FreeIPA server components are:
- MIT Kerberos KDC – Provides Single-Sign-on authentication solution
- 389 Directory Server – Main data store and provides a full multi-master LDAPv3 directory infrastructure.
- ISC Bind DNS server – Bind is the default Domain name resolution service in FreeIPA.
- Dogtag Certificate System – This component provides CA & RA used for certificate management functions.
- NTP Server – For time synchronization across a fleet of nodes joined to the domain
- Web UI / CLI Interface– Used to centrally manage access control, the delegation of administrative tasks, and other network administration tasks.
Minimum hardware requirements when installing FreeIPA Server on Rocky Linux 9 / AlmaLinux 9:
- 4GB RAM
- 2 vCPUs
- FQDN – It must be resolvable from the DNS server configured in the system
- Minimum of 10 GB Disk space availability
Use the commands shared below to check CPU, Memory, and disk space on your Rocky Linux 9 / AlmaLinux 9 instance.
# CPU Cores
$ grep -c ^processor /proc/cpuinfo
4
# Memory check
$ free -h
# Disk space
$ lsblk -fpAdd FreeIPA Server IP address and its DNS name inside the /etc/hosts file:
$ nano /etc/hosts
IP_server greencloud.example.com
IP_client green1.example.comValidate your IP settings:
$ hostname --ip-addressVerify the reverse DNS configuration (PTR records) is set correctly in your DNS Server using the dig command:
$ dig +short -x <ServerIPAddress>3: Install and Configure the FreeIPA server
Next, we install FreeIPA packages on the Rocky Linux 9 / AlmaLinux 9 server. No extra RPM repository is required, all the packages and dependencies are available in default OS default repositories.
Install all FreeIPA server and client packages with the following commands:
dnf -y install freeipa-server freeipa-server-dns freeipa-clientRun the FreeIPA server installer
FreeIPA server configuration is done using the ipa-server-install command line tool. The installer script will create a log file at /var/log/ipaserver-install.log:
ipa-server-installThe script prompts for several required settings and offers recommended default values in brackets.
- To accept a default value, press Enter.
- To provide a custom value, enter the required value.
See below for complete prompts you’ll get during installation and expected responses:
$ ipa-server-install
The log file for this installation can be found in /var/log/ipaserver-install.log
==============================================================================
This program will set up the IPA Server.
Version 4.10.2
This includes:
* Configure a stand-alone CA (dogtag) for certificate management
* Configure the NTP client (chronyd)
* Create and configure an instance of Directory Server
* Create and configure a Kerberos Key Distribution Center (KDC)
* Configure Apache (httpd)
* Configure SID generation
* Configure the KDC to enable PKINIT
To accept the default shown in brackets, press the Enter key.
Do you want to configure integrated DNS (BIND)? [no]: press enter
Enter the fully qualified domain name of the computer
on which you're setting up server software. Using the form
<hostname>.<domainname>
Example: master.example.com.
Server host name [greencloud.example.com]: press enter
The domain name has been determined based on the host name.
Please confirm the domain name [example.com]: press enter
The kerberos protocol requires a Realm name to be defined.
This is typically the domain name converted to uppercase.
Please provide a realm name [EXAMPLE.COM]: press enter
Certain directory server operations require an administrative user.
This user is referred to as the Directory Manager and has full access
to the Directory for system management tasks and will be added to the
instance of directory server created for IPA.
The password must be at least 8 characters long.
Directory Manager password: <Directory-Manager-Password>
Password (confirm): <Confirm-Directory-Manager-Password>
The IPA server requires an administrative user, named 'admin'.
This user is a regular system account used for IPA server administration.
IPA admin password:
Password (confirm):
Do you want to configure chrony with NTP server or pool address? [no]: press enter
The IPA Master Server will be configured with:
Hostname: greencloud.example.com
IP address(es): IP_server
Domain name: example.com
Realm name: EXAMPLE.COM
The CA will be configured with:
Subject DN: CN=Certificate Authority,O=EXAMPLE.COM
Subject base: O=EXAMPLE.COM
Chaining: self-signed
Continue to configure the system with these values? [no]: yes
The following operations may take some minutes to complete.
Please wait until the prompt is returned.
Disabled p11-kit-proxy
Synchronizing time
Configuration of chrony was changed by installer.
Attempting to sync time with chronyc.
Process chronyc waitsync failed to sync time!
Unable to sync time with chrony server, assuming the time is in sync. Please check that 123 UDP port is opened, and any time server is on network.
Warning: IPA was unable to sync time with chrony!
Time synchronization is required for IPA to work correctly
Configuring directory server (dirsrv). Estimated time: 30 seconds
[1/41]: creating directory server instance
[2/41]: tune ldbm plugin
.....If your FreeIPA server installation on Rocky Linux 9 / AlmaLinux 9 was successful, expect output similar to this:
Open FreeIPA service ports on the firewall
A list of FreeIPA service ports is as listed in the following table:
Let’s open the ports on the firewall using firewall-cmd:
firewall-cmd --add-service={dns,ntp,freeipa-ldap,freeipa-ldaps} --permanent
firewall-cmd --add-port={80,443,389,636,88,46,53}/tcp --permanent
firewall-cmd --add-port={88,464,123}/udp --permanentThen reload firewall configuration for the change to take effect immediately:
firewall-cmd --reloadList allowed services on the firewall:
$ [root@ipa ~]# firewall-cmd --list-all
public
target: default
icmp-block-inversion: no
interfaces:
sources:
services: cockpit dhcpv6-client dns freeipa-ldap freeipa-ldaps ntp ssh
....4: Access FreeIPA Management Dashboard
After installation, the FreeIPA Server web-based administration console can be accessed using the server hostname on https:
https://greencloud.example.comIgnore the SSL warning by clicking “Advanced” > “Proceed to ipa.example.com (unsafe)“
Login with the admin username and password set during installation.
Upon successful login you’re presented with an interface that has such the look:
5: Manage FreeIPA using the CLI Interface
The ipa command can be used to perform all FreeIPA server operations. But first, get the admin user Kerberos ticket:
$ kinit admin
Password for [email protected]:The time validity of the assigned ticket can be checked using klist:
$ klist
Ticket cache: KCM:0
Default principal: [email protected]
Valid starting Expires Service principal
03/22/24 05:10:14 03/23/24 04:27:26 krbtgt/[email protected]Set the user’s default shell to /bin/bash.
$ ipa config-mod --defaultshell=/bin/bash
Maximum username length: 32
Home directory base: /home
Default shell: /bin/bash
Default users group: ipausers
Default e-mail domain: example.com
Search time limit: 2
Search size limit: 100
User search fields: uid,givenname,sn,telephonenumber,ou,title
Group search fields: cn,description
Enable migration mode: FALSE
Certificate Subject base: O=EXAMPLE.COM
Password Expiration Notification (days): 4
Password plugin features: AllowNThash, KDC:Disable Last Success
SELinux user map order: guest_u:s0$xguest_u:s0$user_u:s0$staff_u:s0-s0:c0.c1023$unconfined_u:s0-s0:c0.c1023
Default SELinux user: unconfined_u:s0-s0:c0.c1023
Default PAC types: MS-PAC, nfs:NONE
IPA masters: greencloud.example.com
IPA CA servers: greencloud.example.com
IPA CA renewal master: greencloud.example.com
IPA master capable of PKINIT: greencloud.example.comTest by adding a user account and listing accounts present:
$ ipa user-add test --first=Test --last=User [email protected] --password
Password:
Enter Password again to verify:
-------------------
Added user "test"
-------------------
User login: test
First name: Test
Last name: User
Full name: Test User
Display name: Test User
Initials: TU
Home directory: /home/test
GECOS: Test User
Login shell: /bin/bash
Principal name: [email protected]
Principal alias: [email protected]
User password expiration: 20210802153038Z
Email address: [email protected]
UID: 933400003
GID: 933400003
Password: True
Member of groups: ipausers
Kerberos keys available: TrueTo list user accounts added, run:
$ ipa user-find
---------------
2 users matched
---------------
User login: admin
Last name: Administrator
Home directory: /home/admin
Login shell: /bin/bash
Principal alias: [email protected]
UID: 1201400000
GID: 1201400000
Account disabled: False
User login: test
First name: Test
Last name: User
Home directory: /home/test
Login shell: /bin/bash
Principal name: [email protected]
Principal alias: [email protected]
Email address: [email protected]
UID: 1201400001
GID: 1201400001
Account disabled: False
----------------------------
Number of entries returned 2
----------------------------




