Configuring BitLocker to Encrypt Data on Windows Server 2022
1. Introduction
BitLocker is a disk encryption feature available on Windows Server 2022 that helps protect data from unauthorized access in case of disk loss or theft. This technology uses the Advanced Encryption Standard (AES) algorithm to secure data.
2. Prerequisites
Before installing and configuring BitLocker, ensure the following conditions are met:
- The server is running Windows Server 2022.
- A TPM (Trusted Platform Module) version 2.0 (or use the non-TPM mode) is available.
- Administrator privileges on the server.
- The operating system is updated with the latest patches.
- The disk to be encrypted must have at least two partitions (one system partition and one data partition).
3. Installing BitLocker
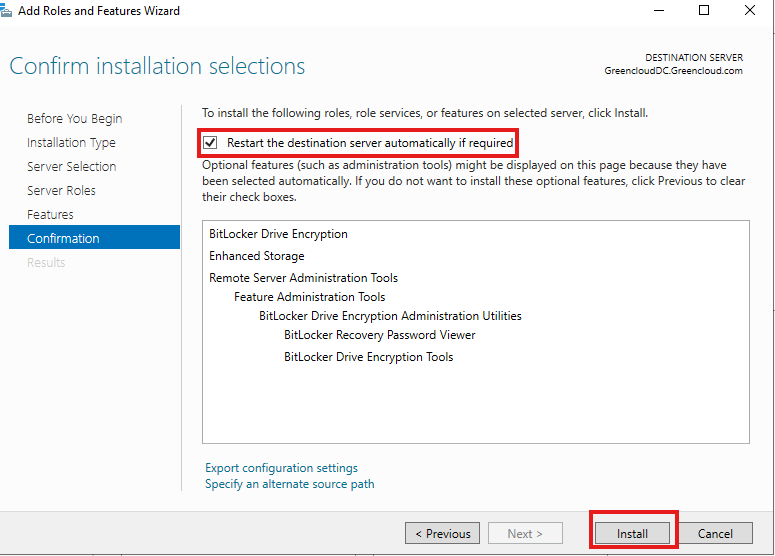
Step 1: Install BitLocker
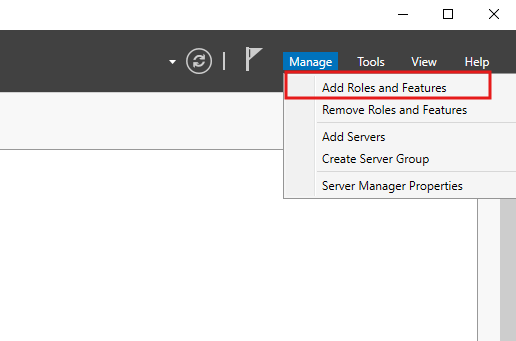
Open Server Manager.
-
Select Manage > Add Roles and Features.
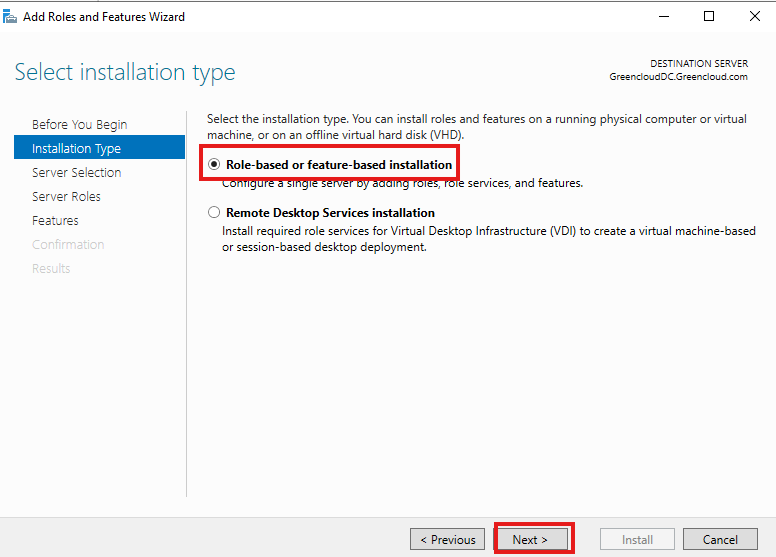
Choose Role-based or feature-based installation and click Next.
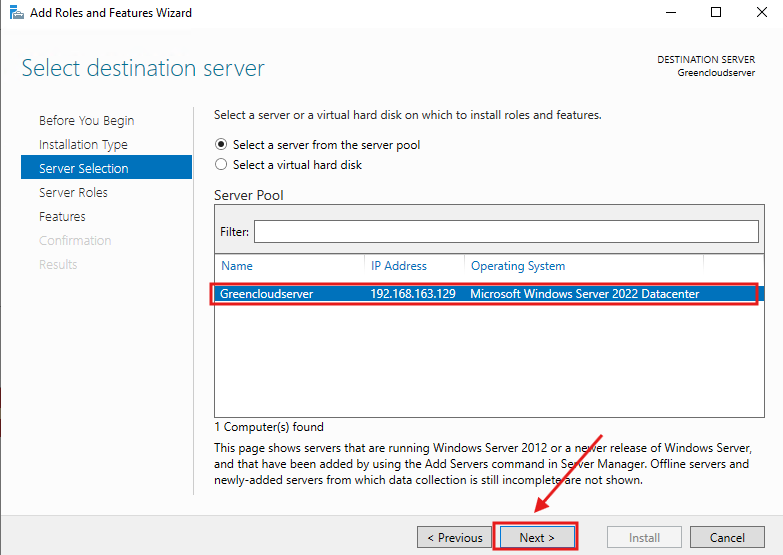
3. Select the destination server and click Next.
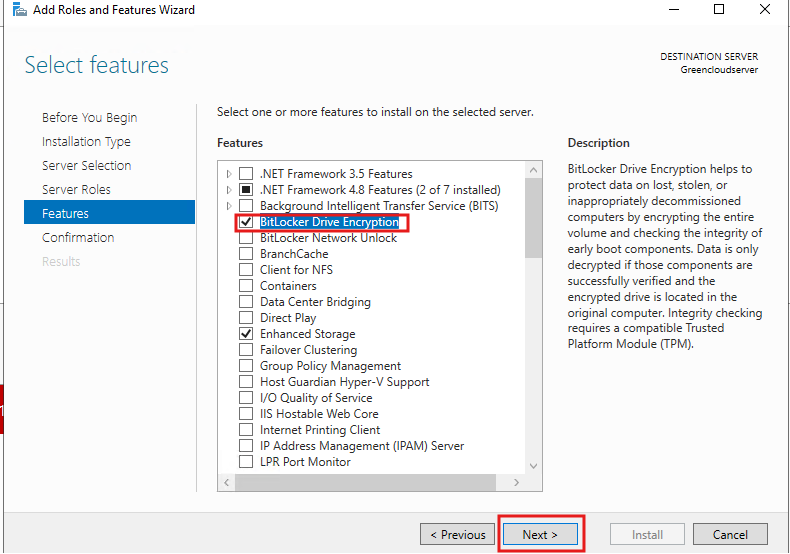
4. In the Features section, select BitLocker Drive Encryption.
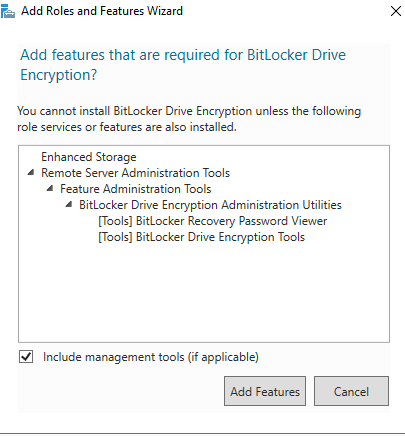
5. Check Include management tools, then click Next.
Click Install and wait for the installation to complete.
Restart the server if prompted.
Step 2: Enable BitLocker Encryption
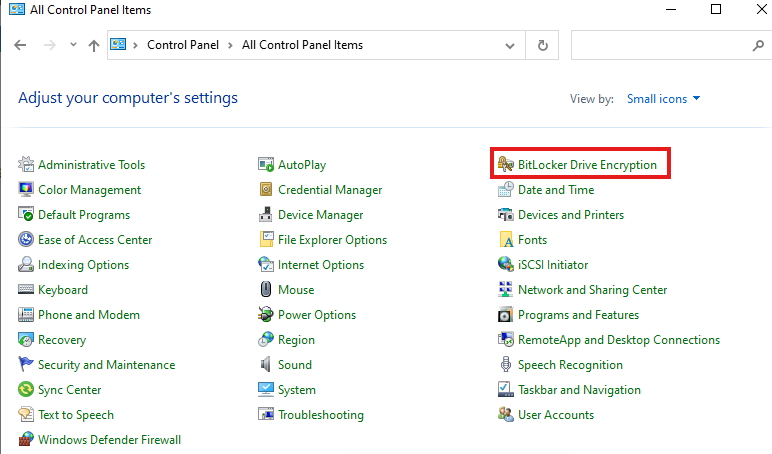
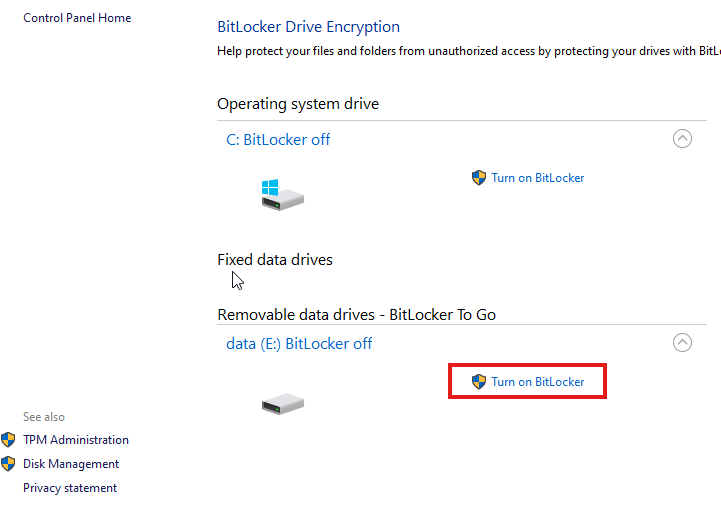
- Open Control Panel > BitLocker Drive Encryption.
2. Select the drive to be encrypted and click Turn on BitLocker.
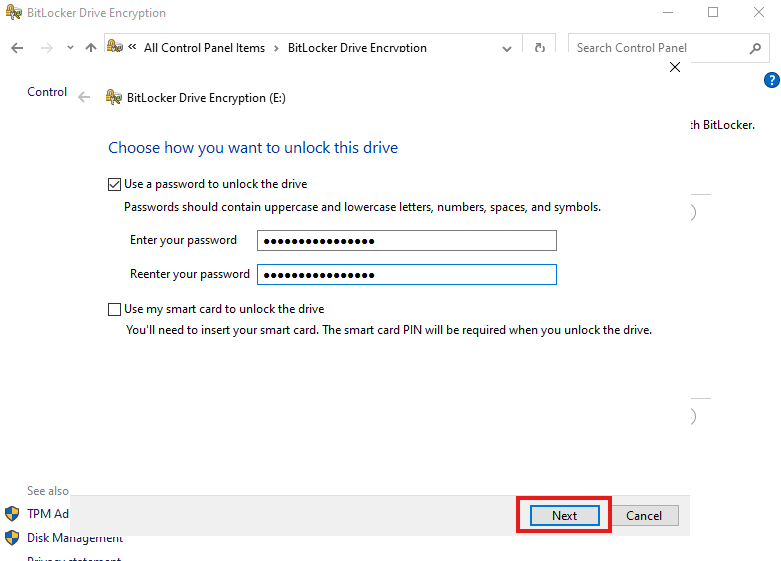
3. Choose an unlocking method:
-
- Password: Enter a strong password to unlock.
- Smart card: Use the smart card to unlock.
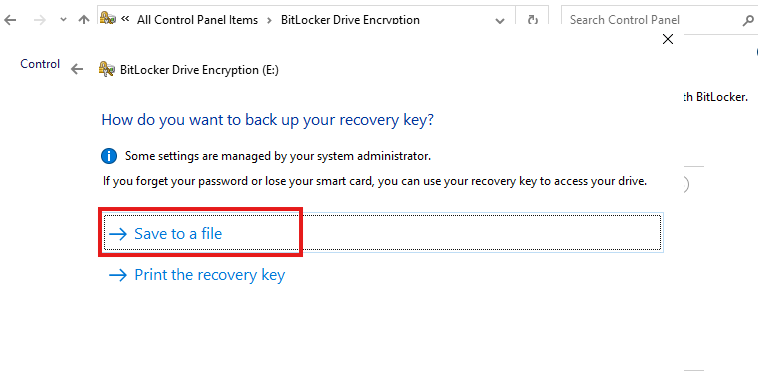
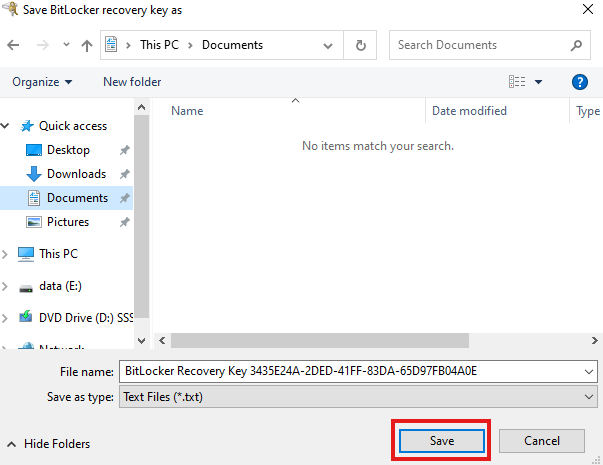
4. Save the recovery key in a secure location (USB, file, or Microsoft account).
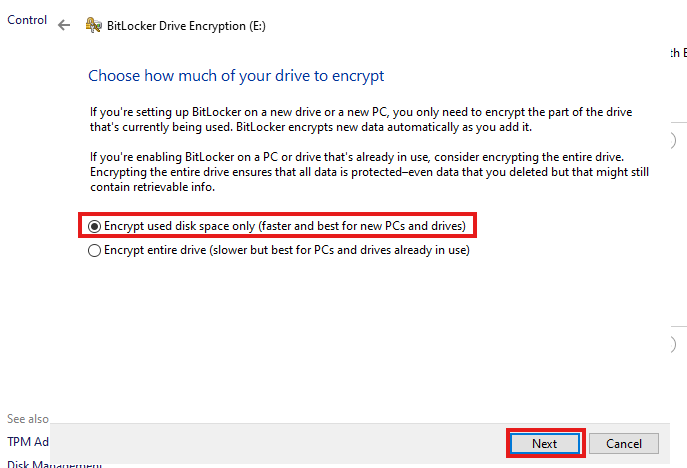
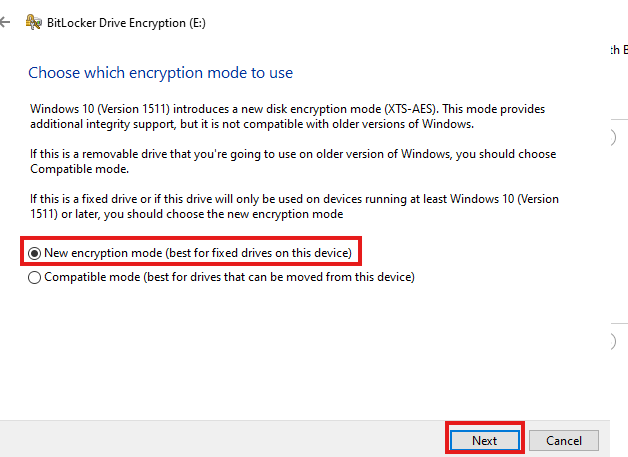
5. Select the encryption mode:
-
- New encryption mode: Recommended for new drives.
- Compatible mode: For portable or legacy systems.
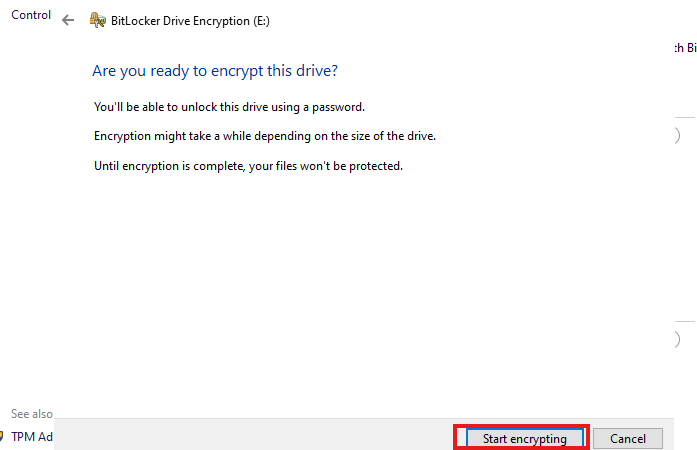
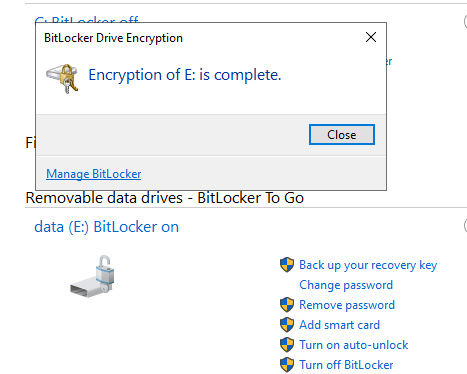
6. Click Start Encrypting and wait for the process to complete.
Step 3: Verify BitLocker Status
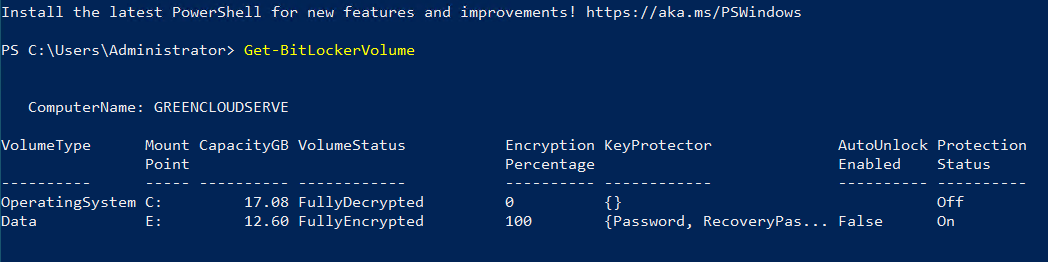
1. Check BitLocker status using:
Control Panel > BitLocker Drive Encryption to view drive status.
PowerShell command:
Get-BitLockerVolume
2. Managing BitLocker with PowerShell
Use PowerShell commands to manage BitLocker:
Enable BitLocker:
Enable-BitLocker -MountPoint "E:" -EncryptionMethod Aes256 -UsedSpaceOnly - -PasswordProtector
Check BitLocker status:
Get-BitLockerVolume
Retrieve recovery key:
manage-bde -protectors -get E:
Step 4: Enable BitLocker to Require a Password for RDP Login
1. Disable Auto-Unlock
To prevent BitLocker from automatically unlocking the drive after startup:
Run the following command in PowerShell (Administrator):
manage-bde -autounlock -disable E:
2. Automatically Lock the E: Drive Upon Logout
By default, when you reconnect via RDP, BitLocker keeps the drive unlocked. To force it to lock upon logout:
Create a script to lock the drive when logging out automatically:
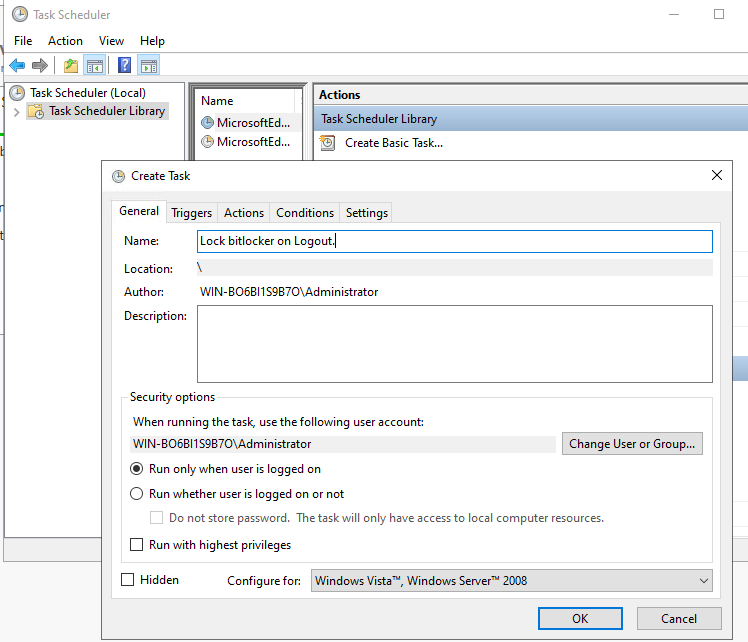
2.1 Open Task Scheduler (taskschd.msc).
2.2 Click Create Task.
2.3 Name the task: Lock BitLocker on Logout.
2.4 Go to the Triggers tab > Click New… > Select “On disconnect from user session”.
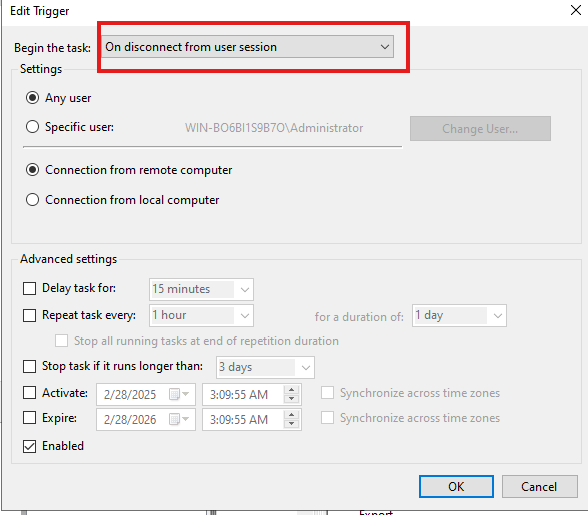
-
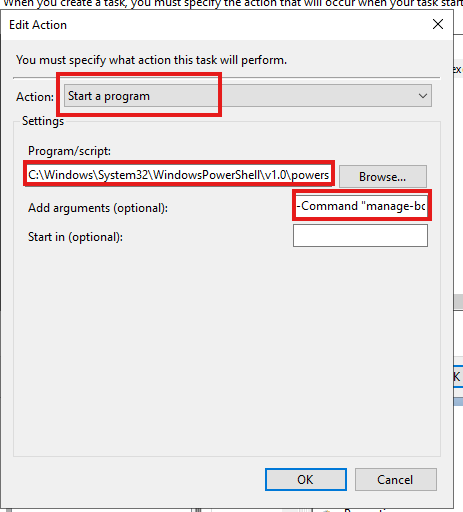
- Action: Start a program
- Program/script: C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe
- Add arguments:-Command “manage-bde -lock C: -ForceDismount”
2.6 Click OK to save.
Result: Whenever you log out or lose the RDP connection, the E: drive will automatically lock, requiring password entry for access.
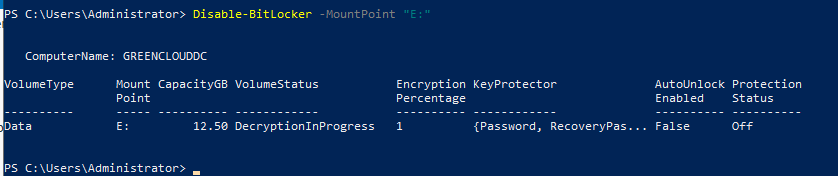
Disable BitLocker:
Run the following command in PowerShell (Administrator):
Disable-BitLocker -MountPoint "E:"
Conclusion
BitLocker is a powerful security solution that helps protect data on Windows Server 2022. Implementing BitLocker prevents unauthorized access and secures data in case of loss or theft.
Following this guide, you can easily install and configure BitLocker to ensure data security. Additionally, using GPO to manage BitLocker enhances security and standardization in enterprise environments.

 Choose Role-based or feature-based installation and click Next.
Choose Role-based or feature-based installation and click Next.